Listen to an audio version of this blog by our tech friend, AI
The long-standing debate between security and flexibility in Enterprise WAN architectures has come to an end. Secure networking for modern enterprises is now available with SCION Secure Access Groups.
In today’s interconnected, geopolitical and AI-driven world, WAN architecture is no longer an IT trade-off between security and flexibility, but a strategic business continuity decision. For enterprises evaluating SD-WAN vs MPLS, a third option has emerged.
Existing solutions like MPLS, SD-WAN and VPNs no longer fit the bill. That is why we are offering a fundamentally different approach with Anapaya EDGE’s newest feature SCION Secure Access Groups.
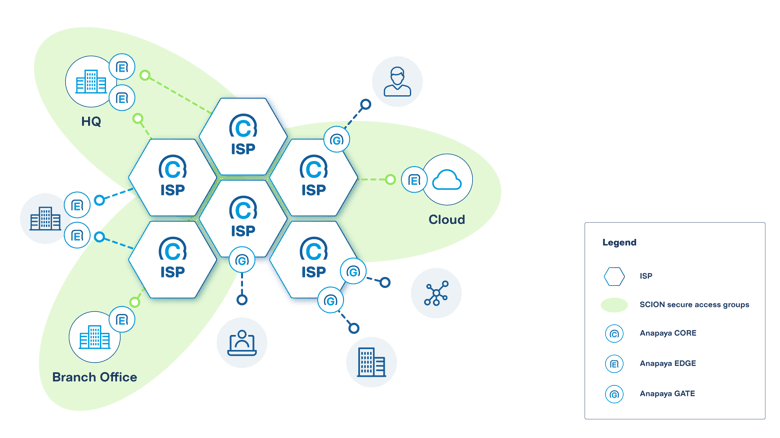
SCION Secure Access Groups lets you build a private, invite-only WAN designed for modern enterprises that need strong isolation with the flexibility needed for hybrid cloud integrations, partner connectivity, and a global footprint.
This is not an incremental improvement; it is a necessary architectural correction for Enterprise WAN security. The industry has spent decades layering security on top of a fundamentally untrustworthy Internet or moved to fully closed networks that do not scale.
We are flipping that model with SCION Secure Access Groups. By leveraging this new feature in Anapaya EDGE, companies can build a next-generation Enterprise WAN on the SCION Internet that makes entire networks invisible while increasing cyber resilience, provider diversity, and operational efficiency.
Why are enterprises replacing MPLS, SD-WAN, and VPNs?
Most Enterprise WANs are built using MPLS, SD-WAN, and VPNs – or a combination of these. While these approaches address important aspects of enterprise connectivity, they also force a choice between security and flexibility.
MPLS provides strong isolation and predictable performance. However, this solution comes with well-known limitations:
- High cost for dedicated lines
- Limited flexibility and operational complexity when integrating third parties
- Dependency on a single provider, creating concentration risk and vendor lock-in
- Endpoints and paths remain discoverable on the Internet, opening up multiple venues for cyberattacks
- Perimeter devices such as firewalls and VPNs are high-value targets; amplified by AI accelerating the exploitation of zero-day vulnerabilities, the time between exposure and compromise is shrinking from months to days
- Enterprises have no control over routing paths, leading to traffic potentially routing through congested paths, untrusted jurisdictions, or single points of failure, challenging the overall resilience of the business
Ultimately, the biggest strategic gap in MPLS and SD-WAN is that they are typically provided by a single vendor, creating a supply-chain risk and potentially a single point of failure. Once again, these kinds of setups impact the cyber resilience of the whole business or organization.
How does SCION compare to MPLS, SD-WAN, and VPNs?
We compare SCION Secure Access Groups with MPLS, SD-WAN, and VPNs across eight operational and technical dimensions for an overview of the key differences to consider in the decision-making process when selecting an Enterprise WAN solution.
Security model
Attack surface
DDoS protection
Provider lock-in
Failover
Cloud/hybrid ready
Path control
Cost
MPLS
Isolated private lines
Low
High
Yes, single provider
Automated, fast
Complex & expensive
Full control by provider
High (dedicated lines)
SD-WAN / VPN
Overlay on public Internet
High, discoverable endpoints
None
Yes for SD-WAN only
Automated, but slow due to Internet latency
Yes
Limited
Medium
SCION SAG
Invisible at network layer
Low
Built-in by design
No, multi-provider
Automated, multi-path
Yes
Full control by user
Lower than MPLS and SD-WAN
Introducing SCION Secure Access Groups for modern businesses
SCION Secure Access Groups allows enterprises to design a WAN that is private yet flexible, enabling them to securely connect branch offices, headquarters, data centers, cloud environments, and partners over the SCION Internet.
Security is enforced directly at the network layer on the SCION Internet, rather than added on top of the public Internet. Only explicitly authorized entities can exchange traffic, all communication is encrypted (thanks to EDGE-to-EDGE encryption), and data follows cryptographically validated paths defined by the enterprise.
From a tech view, this is what enterprise networking should have looked like all along: closed yet flexible by default, provably trustworthy, and designed for security and cyber resilience. Instead of hoping overlays and encryption will save us, SCION removes entire classes of risk without compromising flexibility.
As a result, enterprise WANs built with SCION Secure Access Groups, a feature of Anapaya EDGE, are invisible to unauthorized networks, resistant to cyberattacks, and independent of any single provider.
How to build your Enterprise WAN with SCION Secure Access Groups
What is SCION Secure Access Groups?
SCION Secure Access Groups is a feature of Anapaya EDGE that fundamentally changes how private enterprise networks are built over the SCION Internet.
Instead of exposing network endpoints and then securing them with overlays (as is common with VPNs or SD-WAN), SCION Secure Access Groups allows enterprises to form invite-only private groups within existing SCION networks.
Only explicitly authorized participants are allowed to join a group. Communication is strictly limited to members of the same group; anyone outside the group cannot see the network, its endpoints, or the paths traffic takes.
This is delivered by the Anapaya Hidden Segment Directory (HSD), a dedicated network service where private SCION path segments are registered. This service can be provided by us at Anapaya, third-parties, or the enterprise itself.
How does SCION Secure Access Groups work?
Whether you are planning an MPLS migration or evaluating SD-WAN alternatives, deployment follows three steps.
STEP 1: Install Anapaya EDGE across your ecosystem to enable SCION connectivity, including offices, data centers, cloud environments, and partner sites.
STEP 2: Register private paths in the Hidden Segment Directory (Anapaya HSD) where they are made visible only to authorized group members.
STEP 3: Manage policies, from access control to group membership and routing policies, via the Anapaya CONSOLE, a centralized and intuitive management platform.
Why deploy SCION Secure Access Groups for your Enterprise WAN?
With SCION Secure Access Groups, you can now replace legacy VPN, MPLS, and SD-WAN systems with a single, SCION-powered architecture. The benefits for your enterprise are:
-
Reduced attack surface: All the data within the Enterprise WAN is invisible to unauthorized entities, as well as the paths, preventing cyberattacks such as DDoS and ransomware.
-
Cyber-resilience: A multi-provider set-up eliminates concentration risk and single points of failure. In parallel, SCION’s multi-path capability enables seamless failover by switching traffic automatically if a path becomes unavailable.
-
Easy technical installation: Private, multi-AS enterprise networks can be deployed over the SCION Internet with minimal operational complexity and an intuitive user experience.
-
Simplified management: Centralized, user-friendly management via the Anapaya CONSOLE.
-
Scalable and flexible: The architecture of the Enterprise WAN scales on demand, allowing new entities to be added without operational complexity.
-
Cost-efficient: More economical than private lines, SD-WAN, and VPNs solutions.
In summary, compared to MPLS, SCION Secure Access Groups provides the same isolation with the added bonus of a multi-provider configuration for lower concentration risk and more flexibility. Compared to SD-WAN and VPNs, SCION Secure Access Groups enforces security at the network layer on the SCION Internet, making business critical applications invisible to unauthorized entities. While SD-WAN benefits include centralized management and lower bandwidth costs, it cannot match SCION’s architectural security.
In the short term, SCION Secure Access Groups requires investment in learning a new technology, in the long term, it provides advantages for specific use cases that need to be able to ensure connectivity across multiple locations in all security.
To illustrate this, the following section outlines two enterprise use cases for SCION Secure Access Groups.
SCION Secure Access Groups: Use cases for Enterprise WANs
Private multi-cloud network at a bank
Let’s take a network administrator at a bank who is responsible for ensuring that their critical systems are secure and operational.
The bank's infrastructure spans multiple environments: an on-premises data center hosting core systems, alongside deployments in AWS and Azure.
Traditionally, connecting these environments would require exposing endpoints to the public Internet or relying on private networks that increase operational complexity and costs.
By creating a SCION Secure Access Group, the administrator can define a private trust domain that includes only the organization’s own Autonomous System (AS): on-premises, AWS, and Azure.
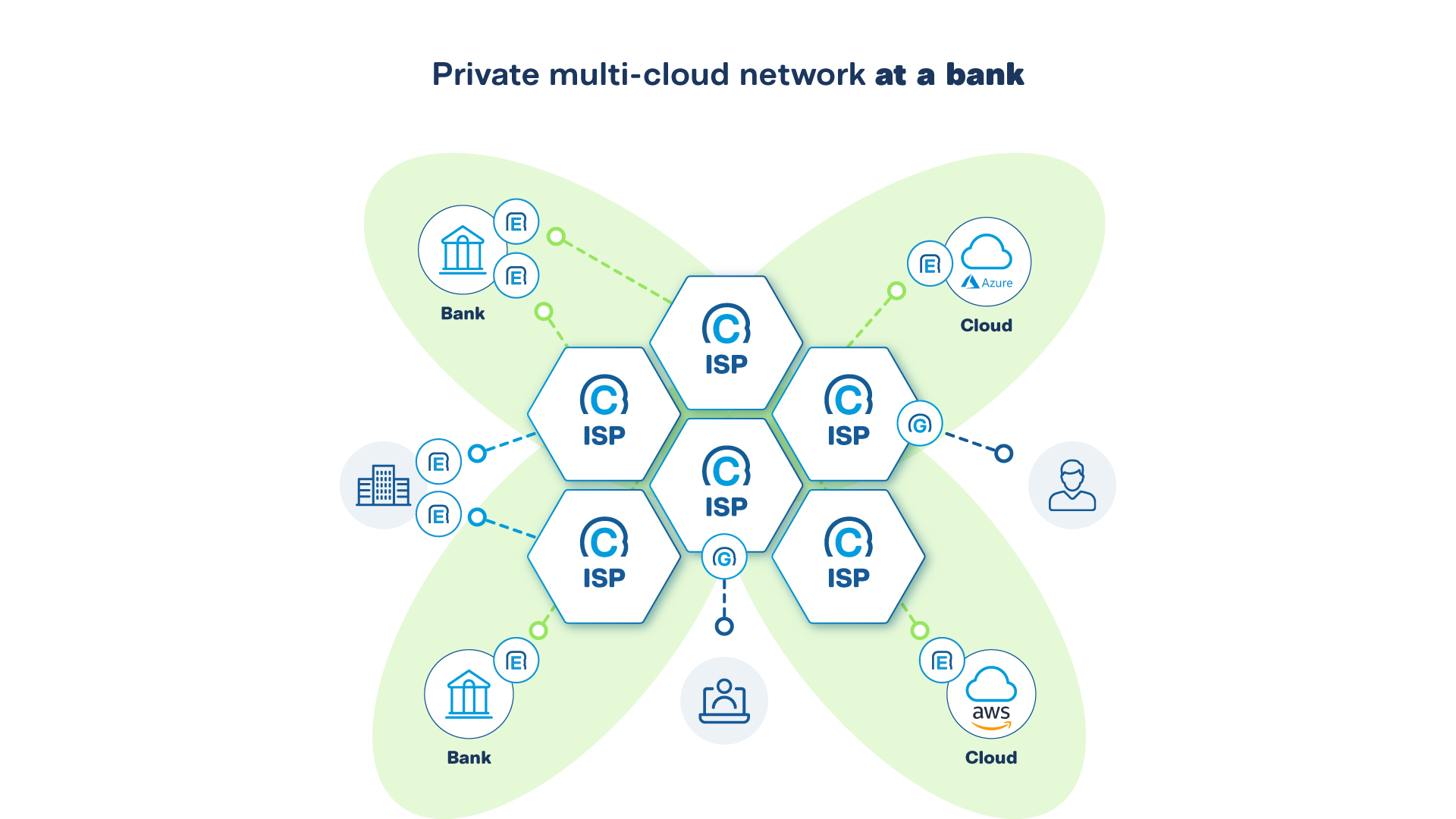
Traffic within the group is completely invisible to the public SCION Internet outside this group and, most importantly, to the wider Internet. There are no publicly reachable endpoints, and no external visibility, all the while the multi-provider set up ensures resilience.
The result is a multi-cloud network that functions like a private backbone.
Secure connectivity between a hospital and its suppliers
A hospital collaborates with external suppliers such as pharmacies, laboratories, and medical device providers to support patient care. These interactions include the exchange of prescriptions, lab results, and patient data. All data is highly sensitive and must be protected against unauthorized access, tampering, and any exposure to the public Internet.
Using SCION Secure Access Groups, the hospital network administrator can create a dedicated and isolated trust domain that includes only the hospital’s Autonomous Systems and the specific supplier systems required for each workflow. Each supplier is explicitly invited into the Secure Access Group, with access limited to the exact services and data they are authorized to see and use.
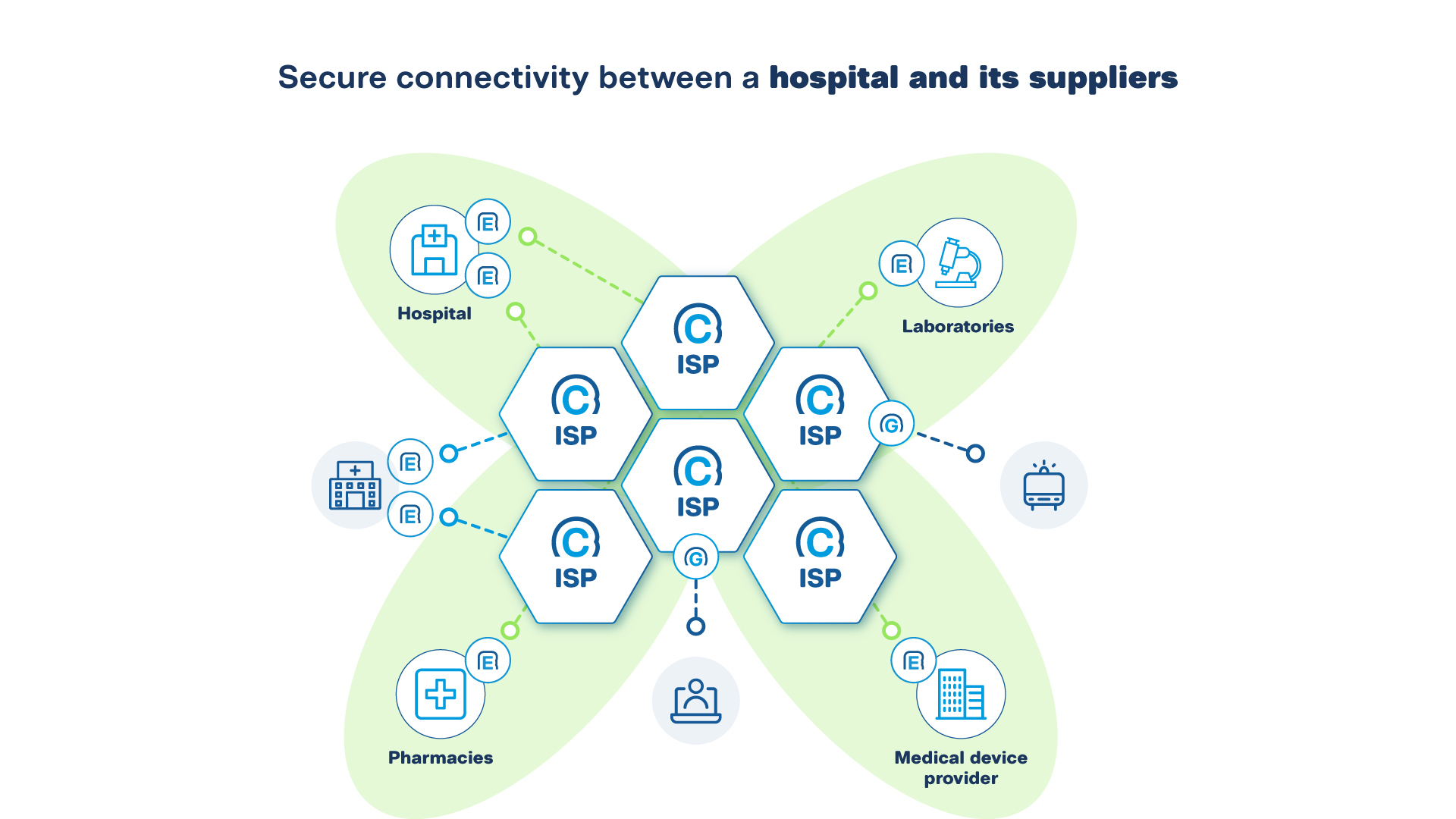
In this configuration, traffic within the SCION Secure Access Group is completely invisible to the public SCION Internet and to the Internet, eliminating endpoint visibility, thus reducing the likelihood of cyberattacks such as DDoS and ransomware.
What the hospital ends up with is a multi-partner network that is the equivalent of a private infrastructure.
How is SCION Secure Access Groups different from a typical SCION network?
SCION Secure Access Groups leverages existing SCION isolation domains instead of requiring the creation of a dedicated SCION isolation domain. The creation of a dedicated isolation domain is suggested for highly critical infrastructures where disruptions have an impact on society.
SCION Secure Access Groups for Enterprise WANs preserves all core SCION benefits, including path control, cryptographic verification, and multi-provider resilience, while simplifying deployment. This is a solution for modern businesses who are constantly changing and evolving their operations, footprint, and growth venues.
Enterprise WAN for modern businesses beyond MPLS SD-WAN, and VPNs
Secure networking must go hand in hand with the ever-changing needs of today’s businesses, without compromising security or flexibility. Fulfilling only one of the two is no longer enough. At the same time, IT is now much more than just a technical consideration; today’s leaders need to think about cyber resilience and readiness for the future.
Geopolitical dynamics, vendor lock-in, and reliance on just a few IT providers have become risks for leaders seeking sustainable enterprise solutions, risks that are present in current solutions.
In addition, the ever-expanding attack surface of today’s Internet, further amplified by AI, increases exposure to cyberattacks with financial and reputational repercussions on organizations.
Combining IT needs with business and strategic considerations is a must. SCION Secure Access Groups addresses all three, providing peace of mind for both IT departments and business leaders.
Frequently Asked Questions
How does SCION Secure Access Groups compare to MPLS and SD-WAN?
How does SCION Secure Access Groups work?
Can SCION Secure Access Groups connect multi-cloud environments securely?
Is SCION Secure Access Groups suitable for partner connectivity?
What is the difference between SCION Secure Access Groups and a SCION isolation domain?
.jpg)

.jpg?width=380&name=Header%20(1).jpg)



.png?width=380&name=Image%20(11).png)



